Preparing for the (Inevitable) Data Breach 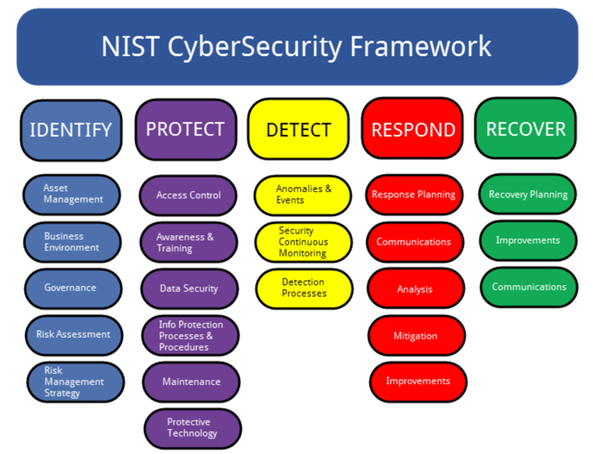 An estimated 70% of Canadian businesses have been victims of a cyber-attack. It is not as much of a question of if but rather when your business may face its own cyber-attack. Startups, in particular, are especially vulnerable, given the limited number of resources available. With margins being consistently thin, a data breach may be the difference between success and failure. It is, therefore, crucial that you’re aware of the risks and how to best mitigate them. Cyber incidents typically occur for the following three reasons[1]:
The fallout from a cyber attack is best mitigated by being prepared and being aware of the protocols and responses that ought to be triggered. The NIST Framework outlines five core competencies (shown in the diagram below) underpinning any comprehensive cybersecurity policy.[2] I suggest that as a startup, you may want to be most focused on the identification stage of the NIST framework so that you’re able to assess what needs priority protection given the likely limited funds available. The following steps help outline the approach that organizations need to adopt to create an effective cybersecurity policy. 1. Governance Team: the executive needs to determine which departments, and which individuals from within those departments need to be assembled on the cyber governance team. A team leader should be appointed. Efforts of the team should be reported to a specialized committee or the board itself to ensure that they are addressing organization-wide concerns relating to potential cybersecurity threats. Understand your requirements under PIPIDA. I have written a more extensive article on how PIPEDA affects you and your business. In short, it applies to most private sector organizations operating in Canada. For more information, see this blog post. 2. Current Inventory: Once a governance team is established, it needs to make an accurate inventory of its data and information system. This inventory should include where the physical systems are located, which information is on it, and who has permission to access it. It should also specify any obvious existing vulnerabilities. The key here is to recognize what your systems are so that you can adequately do a full risk assessment in the next step 3. Risk Assessment: Assess the most common threats that the organization is susceptible to. This could range from malware to phishing attacks. Depending on the complexity of your business and the data it handles, you may wish to seek guidance from a cybersecurity expert to help triage your systems. 4. Target Profile: Upon completion of the risk assessment, your organization should create a target profile and assess where the threat is most likely to stem from. This could include internal threats such as employees being unaware of various phishing or malware threats that may inadvertently expose your system. 5. Determine and Prioritize Gaps: By analyzing the gap between your target and current profile, you’re able to detect any significant discrepancies that need to be addressed by the governance team. 6. Implement Action Plan: Assess deficiencies in the existing cybersecurity regime:
Daniel Frederiks is a member of the BLG Business Venture Clinic and is a second-year law student at the Faculty of Law, University of Calgary. REFERENCES [1] Imran Ahmad, Cybersecurity in Canada: A Guide to Best Practices, Planning, and Management [2] Ibid.
0 Comments
Leave a Reply. |
BVC BlogsBlog posts are by students at the Business Venture Clinic. Student bios appear under each post. Categories
All
Archives
May 2024
|
 RSS Feed
RSS Feed